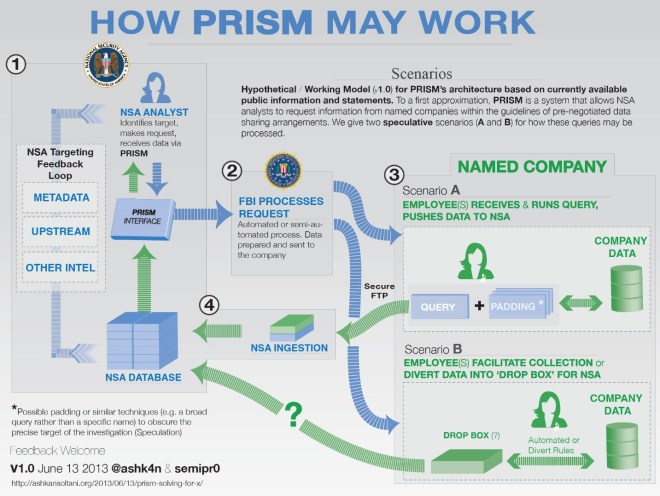
Graph showing the difference in hourly cost between various location tracking techniques.
The Yale Law Journal Online (YLJO) just published an article that I co-authored with Kevin Bankston (first workshopped at the Privacy Law Scholars Conference last year) entitled “Tiny Constables and the Cost of Surveillance: Making Cents Out of United States v. Jones.” In it, we discuss the drastic reduction in the cost of tracking an individual’s location and show how technology has greatly reduced the barriers to performing surveillance. We estimate the hourly cost of location tracking techniques used in landmark Supreme Court cases Jones, Karo, and Knotts and use the opinions issued in those cases to propose an objective metric: if the cost of the surveillance using the new technique is an order of magnitude (ten times) less than the cost of the surveillance without using the new technique, then the new technique violates a reasonable expectation of privacy. For example, the graph above shows that tracking a suspect using a GPS device is 28 times cheaper than assigning officers to follow him. [Read more…]