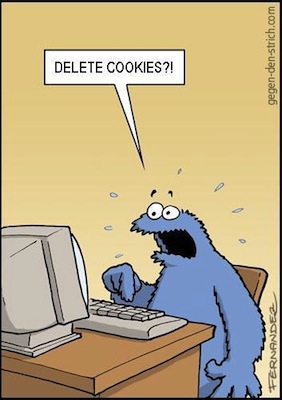
Intelligence agencies follow targets using cookies installed by Google, typically to track users for commercial advertising purposes, to follow suspects online and target them with malware. You can read more about this story here.
PostTV: For NSA, Google cookies allow ‘laser-guided’ targeting
CIR/NPR Collaboration – Your Data and Who Has Access to It
I collaborated with NPR and the Center for Investigative Reporting to develop this script describing who is tracking you throughout your day. The video shows how your digital trail can be assembled into a pretty complete picture of who you are. Some of the script may seem pretty far fetched, but every example was vetted by yours truly and occurs every day (in the US).
You can read the corresponding CIR story here.
NPR’s 4 part series on “All Tech Considered” below called “Your Digital Trail” below:
Part 1: How It Can Be Used Against You
Part 2: Privacy Company Access
Part 3: Does The Fourth Amendment Protect Us?
Part 4: Data Fuels Political And Legal Agendas
Amsterdam Privacy Conference: Behavioural Targeting and Privacy
Amsterdam Privacy Conference
Amsterdam, The Netherlands | October 7-10, 2012
This interdisciplinary panel brought together leading scholars from Europe and the United States to present and discuss recent research on various aspects of behavioural targeting and privacy. Behavioural targeting is the monitoring of people’s online behaviour over time to use the collected information to target people with advertising matching their inferred interests. Using cookies or other tracking technologies, companies compile detailed profiles based on what internet users read, what videos they watch, what they search for etc. Profiles are enriched with up to date location data of users of mobile devices, data that people submit to websites themselves and other data that are gathered on and off line. As the internet plays an ever-larger role in our lives, the profiles will become ever more detailed. The constant stream of articles in the academic literature and popular press on behavioural targeting illustrates the relevance of the subject, which is high on the agenda of regulators in Europe and the United States.
I was a discussant at this event.
Flash Cookies and Privacy II
A detailed technical followup to Flash Cookies and Privacy II, describing the mechanisms behind Hulu/KISSmetrics’ respawning practices
 I thought I’d take the time to elaborate a bit further regarding the technical mechanisms described in our Flash Cookies and Privacy II paper that generated a bit of buzz recently. For a bit of background, I, along with Chris Hoofnagle and Nathan Good, had the honor of supervising Mika Ayenson and Dietrich J. Wambach in replicating our previous 2009 study which found that websites were circumventing user choice by deliberately restoring previously deleted HTTP cookies using persistent storage outside of the control of the browser (a practice we dubbed ‘respawning’).
I thought I’d take the time to elaborate a bit further regarding the technical mechanisms described in our Flash Cookies and Privacy II paper that generated a bit of buzz recently. For a bit of background, I, along with Chris Hoofnagle and Nathan Good, had the honor of supervising Mika Ayenson and Dietrich J. Wambach in replicating our previous 2009 study which found that websites were circumventing user choice by deliberately restoring previously deleted HTTP cookies using persistent storage outside of the control of the browser (a practice we dubbed ‘respawning’).
In our follow up study, we found that Hulu was still respawning deleted user cookies using homegrown Flash and Javascript code present on the Hulu.com site. Additionally, Hulu, Spotify, and many others were also respawning using code provided by analytics firm KISSmetrics.* Hitten Shah, the founder of KISSmetrics, initially confirmed that the research surrounding respawning was correct in an interview with Ryan Singel although he later criticized the findings after a lawsuit was filed.
(*Hulu and KISSmetrics have both ceased respawning as of July 29th 2011)
CyberJungle Radio: KISSMetrics WebTracking
The CyberJungle Radio Show | August 5, 2011
In 2011, I was a guest on CyberJungle Radio at SecurityBsides Las Vegas, the shadow conference to BlackHat Las Vegas. The CyberJungle got my take on the KISSMetrics web tracking spat.
Related Reading
Respawn Redux
Flash Cookies and Privacy II (2011)
Flash Cookies and Privacy (2009)
Flash Cookies and Privacy II: Now with HTML5 and ETag Respawning
In August 2009, the research team published Flash Cookies and Privacy, a paper that demonstrated that popular websites were using Flash cookies to track users. Some advertisers has adopted this technology because it allowed persistent tracking, even where users had taken steps to avoid web profiling. This allowed sites to reinstantiate HTTP cookies deleted by a user, making tracking more resistant to users’ privacy-setting behaviors.
In this followup study, we reassess the flash cookies landscape and examine a new tracking vector, HTML5 local storage and cache cookies via eTags. [Read more…]
Berkeley Law: Browser Privacy Mechanisms Roundtable
Berkeley Law
Berkeley, CA | February 9, 2011
I gave a tutorial on the state of online tracking.
The Federal Trade Commission preliminary staff report, “Protecting Consumer Privacy in an Era of Rapid Change,” called generally for privacy by design, and specifically for a do not track (DNT) system to allow consumers to better control online collection of information. This is a challenging task, because many web interactions require a transfer of information that could be conceived of as “tracking.” The major developers of browsers have all announced implementations of do not track systems recently. The conceptions of DNT have different needs for implementing regulation and have different implications for businesses and consumers. This roundtable explored the contours of the regulations needed to effectuate do not track, the technical options to implement it, and the political and economic implications of do not track systems.
Flash Cookies and Privacy
In August 2009, I and other graduate students at the University of California, Berkeley – School of Law, Berkeley Center for Law & Technology published Flash Cookies and Privacy, a paper that examined of the use of ‘Flash cookies’ by popular websites.
Websites and Cookies
Advertisers are increasingly concerned about unique tracking of users online. Several studies have found that over 30% of users delete first party HTTP cookies once a month, thus leading to overestimation of the number of true unique visitors to websites, and attendant overpayment for advertising impressions.
Mindful of this problem, online advertising companies have attempted to increase the reliability of tracking methods. In 2005, United Virtualities (UV), an online advertising company, exclaimed, “All advertisers, websites and networks use [HTTP] cookies for targeted advertising, but cookies are under attack.” The company announced that it had, “developed a backup ID system for cookies set by web sites, ad networks and advertisers, but increasingly deleted by users. UV’s ‘Persistent Identification Element’ (PIE) is tagged to the user’s browser, providing each with a unique ID just like traditional cookie coding. However, PIEs cannot be deleted by any commercially available antispyware, mal-ware, or adware removal program. They will even function at the default security setting for Internet Explorer.”
United Virtualities’ PIE leveraged a feature in Adobe’s Flash MX: the “local shared object,” also known as the “Flash cookie.” [Read more…]


