In case you spent your weekend watching closing ceremonies and not reading tech news, there was a lot of buzz around a security problem in Apple products. On Friday, Apple released an emergency update for iOS7 that fixed a severe vulnerability in their SSL/TLS implementation on the iPhone.
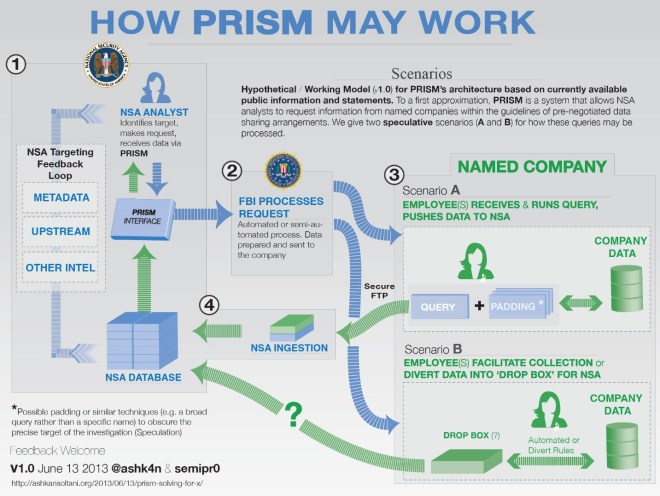
For those who are not technically inclined, SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are the encryption protocols underlying, among many things, the little lock icon you see in the upper right corner of your browser. This encryption protects you from eavesdroppers when logging into any secure site, like your bank account. It also protects you from actors like the NSA (and other governments) scooping up your emails in bulk when you’re … well … anywhere. After Apple released the emergency update for iPhone, security firm CrowdStrike examined the patch and reverse engineered the vulnerabilities it was addressing, only to find out that it repaired some pretty significant parts of the iPhone operating system. They also found that the same vulnerability exists in Apple’s OS X operating system meaning that the problem extends to Mac OS X laptops/desktops, not just iPhones. [Read more…]