Intelligence agencies follow targets using cookies installed by Google, typically to track users for commercial advertising purposes, to follow suspects online and target them with malware. You can read more about this story here.
PostTV: Reporter explains NSA collection of cellphone data
In this video I discuss the NSA’s ability to use massive numbers of cell location records to determine if anyone, including US citizens, are co-traveling with targets of surveillance. You can read more about this story here.
Why Apple’s claim that it can’t intercept iMessages is largely semantics

This op-ed originally appeared in the Washington Post last Saturday in response to Apple’s claims about the security of iMessage.
A lively debate is brewing over the security of Apples iMessages. I was recently quoted on this issue, but Apple has since responded, and it seems important to clarify that the argument now seems to be largely a matter of semantics.
In case you missed it, a group of researchers at Quarklab recently analyzed the iMessage protocol, including the trust model and key exchange, and found some mistakes that leave iMessages open to attacks. I had also previously demonstrated that iCloud backups, including backed-up iMessages, could easily be accessed by Apple. This news is important because previous reports suggested that iMessage encryption was a major impediment to law enforcement, and Apple specifically described iMessage data as “protected by end-to-end encryption so no one but the sender and receiver can see or read them” in response to their reported participation in the NSA’s PRISM program.
Apple stands by its claim that its software can’t be intercepted and that it is not reading iMessages. In that article, Apple spokeswoman Trudy Muller said: “iMessage is not architected to allow Apple to read messages. The research discussed theoretical vulnerabilities that would require Apple to re-engineer the iMessage system to exploit it, and Apple has no plans or intentions to do so.”
But Apple’s response that it cannot intercept messages is a bit misleading.
Apple controls the entire stack: the phone operating system (iOS), iMessage application, the SSL certificates, and key exchange. Quarklab’s researchers demonstrated that if they could obtain (or fake) a trusted Apple SSL certificate AND man-in-the-middle the iMessage key exchange, they would be in a position to intercept or tamper with iMessage. Basically, that means iMessage could be vulnerable if an actor is able to convince the application that they are authorized to carry the data and to insert themselves between the users.
[Read more…]
A Group of Geeks Submitted Questions on NSA Activities
I recently submitted comments to the President’s Review Group on Intelligence and Communications Technologies along with 46 other leading technologists. The mission of this Review Group is to assess whether technological advances, specifically technical data collection capabilities, have undermined the public trust. (Spoiler alert: they have.)
Our comments focused on the need for a technical expert to advise the panel on how online systems work and what the implications are of tapping into them. We also expressed our concern that the NSA’s efforts to subvert encryption and to plant backdoors undermine security for everyone online. Most importantly, our comments include a number of technical questions that we feel this panel should focus on and, when possible, ask that the intelligence community provide answers. You can read the full comments here.
The panel’s work was affected by last week’s government shutdown. It’s not clear how this delay will impact their timeline for a final report, if at all, but I don’t expect to hear answers to our questions soon.
Bits of Freedom: The Dutch Perspective

The Bits of Freedom Crew
I was recently invited to be a visiting fellow at Bits of Freedom in Amsterdam. This was a great opportunity to gain insight into the European privacy debate, not to mention escape the DC summer and visit an amazing city full of bicycles.
Bits of Freedom is a digital rights organization, not unlike the EFF in the United States. They are a mix of lawyers, activists, and tech folk who work at the intersection of technology and human rights. BoF focuses on issues such as transparency, active hacking, net neutrality, and the Transatlantic Trade and Investment Partnership. The staff employ a variety of tools to meet their goals including FOIA, government transparency reports, advocacy campaigns, and direct lobbying to, “influence legislation and self-regulation” both in the Netherlands and across the EU.
My visit focused on learning from the experts here as well as providing some of my own perspective. [Read more…]
Is Electronic Surveillance Out of Control? KCRW’s To The Point
On July 10, I was a guest on KRCW’s daily show, To The Point. Reacting to recent revelations of NSA surveillance issues and comments made by witnesses at the Privacy and Civil Liberties Oversight Board (PCLOB) meeting on Tuesday, I talked about the need for more oversight and transparency of NSA programs by technically minded individuals that can understand the underlying technology and its implications.
Listen to the show. My comments start at about 32 minutes.
Privacy and Civil Liberties Oversight Board
On July 9, I joined a few technical experts on a panel to field questions from the Privacy and Civil Liberties Oversight Board.

The panel footage is available from CSPAN here, with a clip of my remarks here. A draft of my written comments is posted here.
Comments for the Privacy and Civil Liberties Oversight Board
I am speaking today at the PCLOB meeting on Sections 215 and 702 of the PATRIOT Act. My panel begins at 12:30 and you can watch it live here.
I will be commenting on the role of technology in these programs, focused on how the limits of technology suggest that claims that surveillance programs can avoid targeting Americans are probably overstated. [Read more…]
As Technology Changes, So Should Law
Improved technology enabled the NSA’s mass surveillance programs and future improvements will make collecting data on citizens easier and easier.
Recent revelations about the extent of surveillance by the U.S. National Security Agency come as no surprise to those with a technical background in the workings of digital communications. The leaked documents show how the NSA has taken advantage of the increased use of digital communications and cloud services, coupled with outdated privacy laws, to expand and streamline their surveillance programs. This is a predictable response to the shrinking cost and growing efficiency of surveillance brought about by new technology. The extent to which technology has reduced the time and cost necessary to conduct surveillance should play an important role in our national discussion of this issue.
The American public previously, maybe unknowingly, relied on technical and financial barriers to protect them from large-scale surveillance by the government. These implicit protections have quickly eroded in recent years as technology industry advances have reached intelligence agencies, and digital communications technology has spread through society. As a result, we now have to replace these “naturally occurring” boundaries and refactor the law to protect our privacy.
[Read more…]
Computers Freedom and Privacy Conference
Washington DC | June 25, 2013
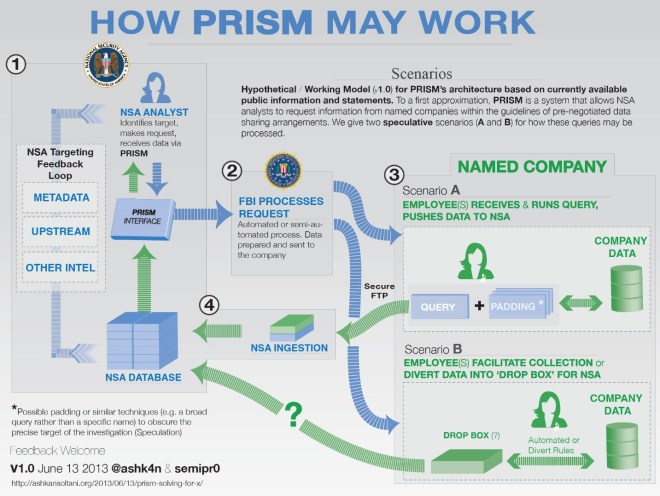
My panel focused on PRISM. We discussed what the program might look like based on publicly available information as well as whether the intelligence gained through the program is worth the risk to American’s privacy.
You can watch the day’s events here. PRISM Panel begins around 2:10:00.
PRISM: Solving for X
I thought it would be a fun exercise to describe PRISM based on information publicly available through the press, private companies, and the DNI. Specifically, how would this system look if we took all the statements made at face value? This might be a stretch, but it seems like a worthwhile exercise — not unlike a multivariate equation when one or more of the variables are unknown.
While PRISM is potentially the least troubling with respect to its legality and the type/volume of information of the 4 programs we’ve learned about, it is also the most technically puzzling. There have been many theories on the architecture of PRISM and I’ve been inundated with requests to help press/advocates understand it — so here goes. [Read more…]